SWIFT
For most of the 1800s, the Rothschild family ran banks in five major European cities1. When one country owed money to another, actual gold didn’t need to be shipped across borders — the Rothschilds just updated their own internal records. ‘France owes Austria this much’ became a note passed between their Paris and Vienna offices.
Because so much money moved through their system, the family could see who was paying whom across all of Europe in real time.
That private clearing role — where one party sits in the middle and tracks who owes what — eventually got taken over by governments and official institutions. First, the Bank of England grabbed control of money issuance in 1844 with the Bank Charter Act2. Then, in 1930, the Bank for International Settlements (BIS) was created to do the same between countries.
This didn’t come out of nowhere. Back in 1892, at the International Monetary Conference in Brussels, Alfred de Rothschild had argued that London’s clearing system was close to ‘perfection’. At the same conference, Julius Wolf suggested building that same kind of system but scaling it up to work between nations. The BIS, founded nearly forty years later, was basically Wolf’s idea materialised.
The packaging changed over time, but the job stayed the same: someone had to sit in the middle of transactions, and whoever did that could see everything flowing through the system.
After World War II, that middle-man job was handled by Telex — essentially a system for sending text messages over dedicated phone lines3. International payments were done by hand, verified with identity codes, and confirmed through back-and-forth messages. It was slow, easy to mess up, and had no encryption. But it was good enough, because there just weren’t that many cross-border payments to process.
But in 1971, the Bretton Woods system collapsed and Nixon took the US dollar off the gold standard4. Currencies started floating against each other, which made international payments far more complicated and far more frequent. On top of that, global trade had already been growing fast through the 1960s, and the Telex system was already buckling under the load.
The Citibank Problem
Into this gap stepped First National City Bank of New York (Citibank). They built their own messaging system called MARTI (Machine Readable Telegraphic Input) to send payment instructions between their London and New York offices5. From 1971 to 1973, they tried to sell access to MARTI as a service other banks could subscribe to.
The banking world said no. The issue was about power: if every bank routed its international payments through one American bank’s system, that bank would be able to see every transaction and would hold enormous leverage over everyone else. It was the same structural problem — whoever carries the messages can see what’s flowing.
So instead, a group of 68 banks from eleven countries across Western Europe and North America decided to build their own system together. In 1971, they hired two research firms — Logica in the UK and the Stanford Research Institute in the US — to figure out whether a shared, cooperatively owned messaging network could actually work. Both studies came back saying yes, it could.
Founding
On May 3, 1973, SWIFT — the Society for Worldwide Interbank Financial Telecommunication — was officially founded as a not-for-profit cooperative under Belgian law6. They put the headquarters in Brussels, which was basically a compromise so that neither New York nor London could claim ownership of it. At launch, 239 banks from fifteen countries signed up as members7.
The idea had its roots in the Société Financière Européenne (SFE), a group of six major banks that had joined forces in 1967 to fund Europe’s investment boom8. The person who actually pushed the concept forward, starting around 1969, was Johannes Kraa, who went on to become SWIFT’s first Board Chairman9.
By late 1974, they had the network design finished. In 1975, they nailed down the basic operating rules and figured out who would be liable if something went wrong. Then on May 9, 1977, Prince Albert of Belgium — who would later become King Albert II — sent the very first SWIFT message10. By that point, membership had nearly doubled: 518 institutions across 22 countries.
Architecture
SWIFT doesn’t actually move money. It moves information about money11. A SWIFT message is basically an instruction from one bank to another — ‘debit this account’, ‘credit that counterparty’, ‘confirm this currency exchange’. The actual money moves separately, through correspondent banking or through clearing systems like TARGET2 in Europe12 and CHIPS in the US13.
SWIFT is the communication layer that sits underneath those settlement systems, not a substitute for them. And because most international transactions ultimately settle in US dollars — which clear through the Federal Reserve — SWIFT effectively acts as the gateway into dollar-based global commerce14. If a bank gets cut off from SWIFT, it loses its standardised way into the correspondent banking network that keeps dollars flowing.
Every institution on SWIFT gets a unique Business Identifier Code15 (BIC); an eight- or eleven-character string which identifies the bank, its country, and its location. Messages follow standardised formats: originally the MT series, now gradually shifting to a newer standard called ISO 20022. That shift isn’t just a technical upgrade. ISO 20022 messages carry much more detailed data16 — purpose codes, beneficiary details, information about who sent the payment — which means that every time the format gets upgraded, whoever can see the messages can see more about each transaction.
Governance
SWIFT is owned by its members — the banks and financial institutions that use it17. Every three years, shareholding gets recalculated based on how many messages each institution sends, so the biggest users get the most voting power.
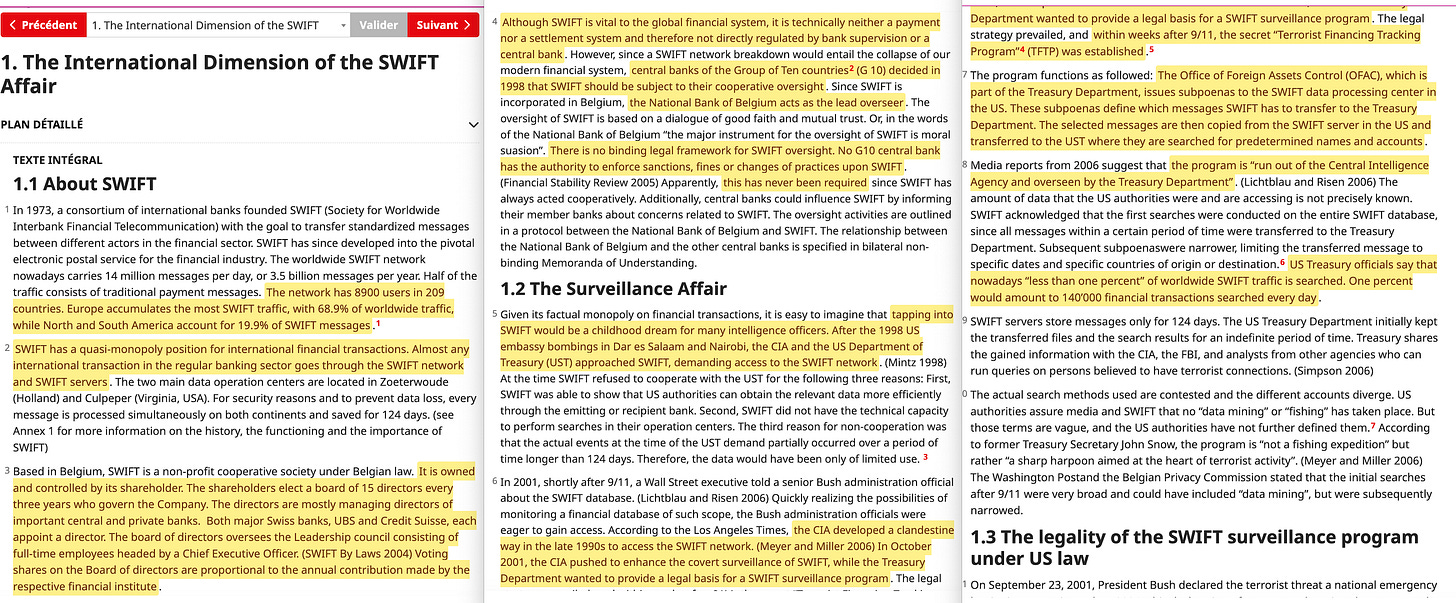
SWIFT isn’t officially classified as a payment system, so it doesn’t get regulated like one. But it’s so important to the global financial system that in 1998, the G10 central banks set up a cooperative oversight arrangement18. The National Bank of Belgium acts as the lead overseer, with formal agreements linking it to the other G10 central banks — the Federal Reserve, Bank of England, European Central Bank, Bank of Japan, and others19.
But none of the G10 central banks can actually fine SWIFT, sanction it, or force it to change anything. SWIFT isn’t directly answerable to any single government. It’s a Belgian cooperative that gets supervised through polite pressure, not legal authority.
SWIFT runs on membership fees and per-message charges, with discounts for high volume. Cutting off a country’s banks means lost revenue. But so far, that tension has never really been tested — every time SWIFT has been asked to disconnect someone, the request has come from Western governments whose banks generate most of SWIFT’s traffic anyway. The people asking for sanctions and the people paying SWIFT’s bills have always been the same group.
The Surveillance Layer
After the 1998 US embassy bombings in Tanzania and Kenya, the CIA and the US Treasury went to SWIFT and asked for access to its messaging data20. SWIFT said no.
Then 9/11 happened, and everything changed. Under a program called the Terrorist Finance Tracking Programme21 (TFTP), SWIFT started handing over transaction data to the US Treasury for counter-terrorism purposes22. This stayed secret until the New York Times broke the story in 2006. It set off a major argument between the US and Europe over data privacy — European leaders wanted to know why American agencies were getting access to European financial records23. The European Parliament actually rejected the agreement at first, but a revised version was negotiated and passed in 2010.
The TFTP turned the messaging system that carried the world’s payment instructions into a surveillance tool. SWIFT’s data — who sent money, who received it, how much, what for, and when — amounted to a detailed map of global financial activity. Anyone with access to that data could watch money move around the world in near real time.
The TFTP agreement is still active today. SWIFT itself lists cooperation with authorities to fight ‘illegal financial activities’ as one of its core functions on its own website.
The Compliance Framework
The surveillance framework that the TFTP made official didn’t appear out of thin air. The legal groundwork had been laid twelve years earlier by an organisation most people have never heard of.
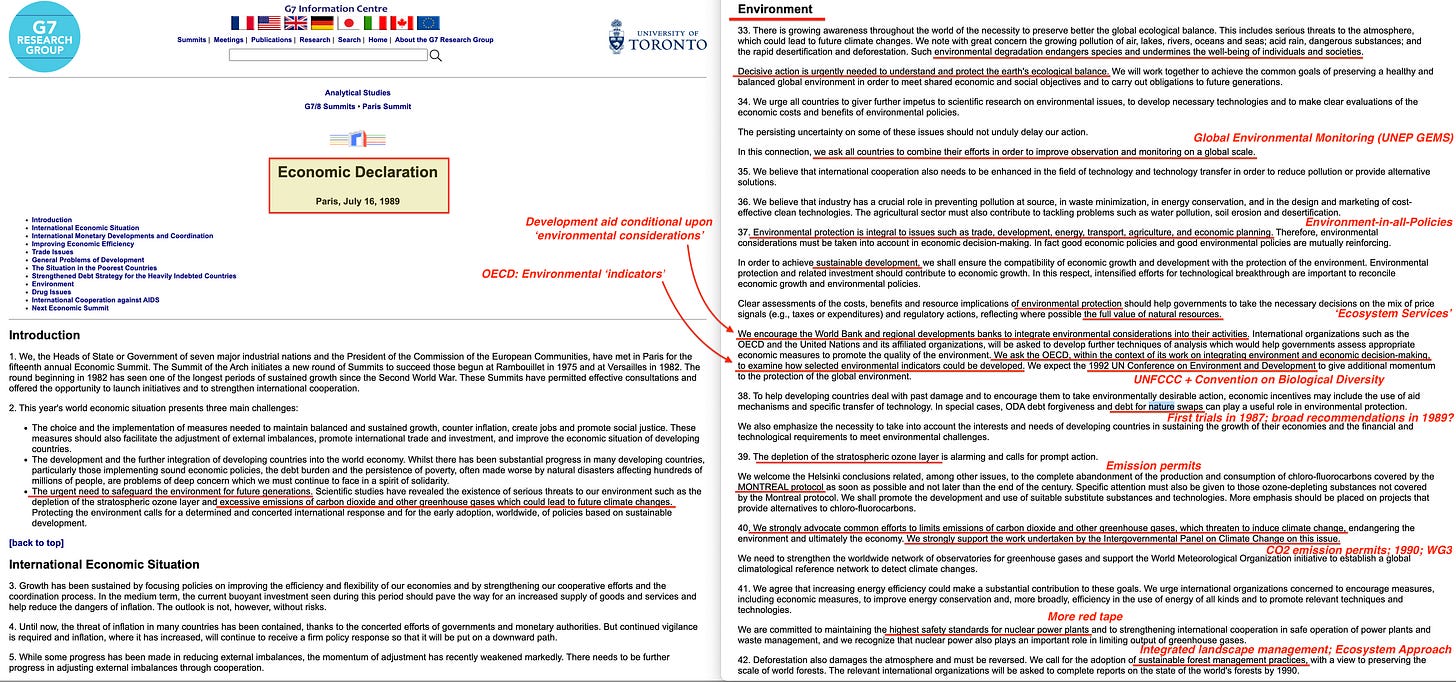
The Financial Action Task Force (FATF) was created at the G7 summit in Paris in July 198924, originally to fight drug money laundering. Notably, it wasn’t established by a treaty — that would have required parliaments to vote on it — the G7 leaders just announced it25. FATF produces forty recommendations that tell banks how to identify their customers, monitor transactions, and flag suspicious activity to governments. Officially, these recommendations are voluntary. In reality, they’re anything but. FATF keeps a ‘grey list’ of countries it considers non-compliant — and any transaction involving those countries gets extra scrutiny from banks worldwide. There’s also a ‘black list’, which effectively locks a country out of international banking altogether.
In 2019, FATF was given an open-ended mandate, meaning it can expand the scope of its rules whenever it wants without needing approval from any parliament or legislature. And it has done exactly that, multiple times.
Every bank on SWIFT has to follow FATF’s rules — or risk getting their whole country greylisted. So the two systems work as one: SWIFT is the pipe that carries the messages, and FATF determines what information has to be inside those messages and what checks a bank must run before sending them. The pipe and the filter inside it were both set up without any parliament voting on either.
The same 1989 G7 summit communiqué that created FATF also endorsed the newly formed Intergovernmental Panel on Climate Change (IPCC), called for what eventually became the UN Framework Convention on Climate Change, and — in paragraph 38 — endorsed debt-for-nature swaps as an environmental tool. The financial surveillance architecture and the environmental governance architecture were born in the same document, at the same meeting, announced by the same leaders.
As environmental standards start hardening into compliance requirements — as ESG metrics get formalised, as climate risk gets built into banking regulations like Basel — there’s nothing in FATF’s structure that would stop those standards from being folded into the existing compliance framework.
FATF decides which countries get to participate in international banking. SWIFT decides which institutions get to send messages. The remaining question is whether that same logic will eventually extend down to individual transactions — and if it does, what mechanism would be used to do it.
The Sanctions Weapon
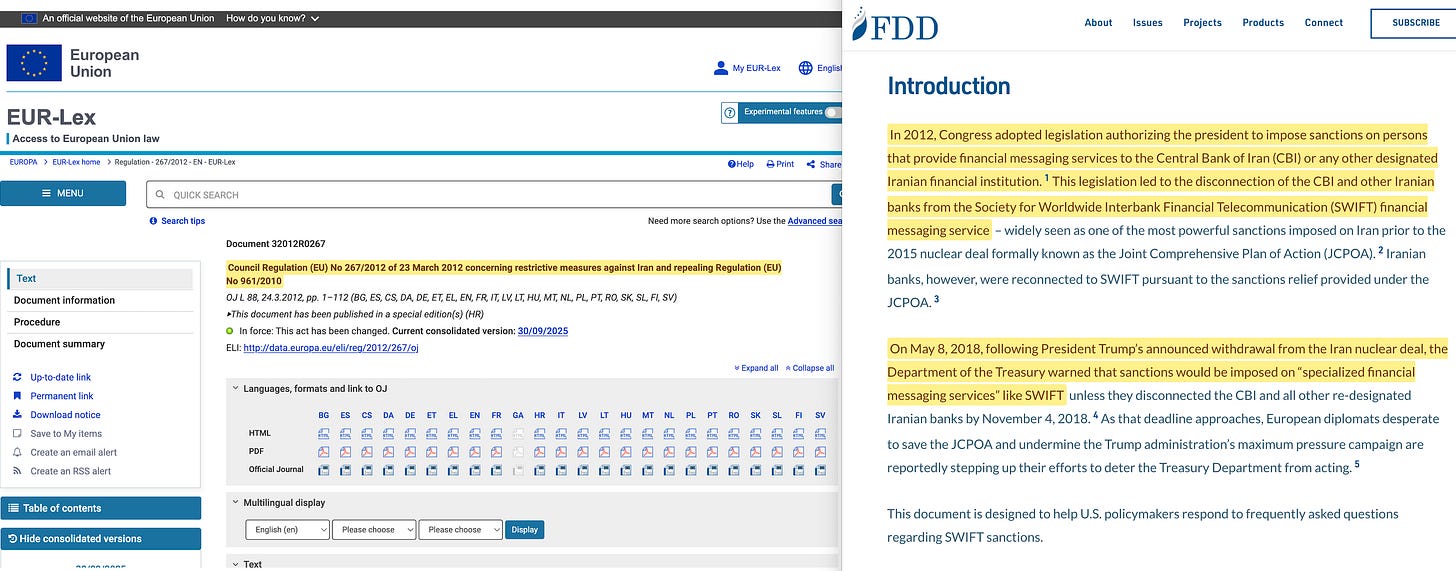
SWIFT was designed to be neutral infrastructure — a cooperative utility, based in a diplomatically neutral country, serving all members equally. That neutrality started cracking in March 201226, when SWIFT disconnected a group of Iranian banks from its network as part of sanctions over Iran’s nuclear program27. The EU passed a regulation banning financial messaging providers from serving sanctioned entities; SWIFT, being a Belgian organisation, had to comply; the board voted to disconnect.
Behind that stood the US Treasury’s Office of Foreign Assets Control28 (OFAC) — any bank that tried to keep processing Iranian payments through workarounds risked losing its own access to dollar clearing through CHIPS and Fedwire.
The impact was immediate. Iran’s ability to make international payments was crippled. Hillary Clinton called it ‘a very effective way of further isolating Iran’29. Former Treasury Secretary Timothy Geithner said the combined effect of SWIFT and oil sanctions was ‘very, very significant’30. French Finance Minister Bruno Le Maire would later describe the idea of doing the same thing to Russia as ‘a financial nuclear weapon’31.
Iran got partially reconnected in 2016 after signing the nuclear deal (the JCPOA), then got cut off again in 2018 when Trump pulled the US out of that agreement.
So the precedent was set — but SWIFT’s board still pushed back against using it freely. When some governments proposed cutting Russia off after it annexed Crimea in 2014, SWIFT pointed to its neutrality mandate, and the idea was dropped.
Eight years later, that resistance was gone. In February 2022, after Russia invaded Ukraine, the EU ordered SWIFT to cut off designated Russian banks32. Seven major banks were disconnected initially, with more added later. Russia adapted — shifting trade to Chinese yuan, expanding its own domestic messaging system33 (SPFS), routing payments through banks in third countries3435 — but everything got more expensive and more difficult as a result.
At this point, the precedent was fully established. Access to SWIFT — and by extension, to dollar-based correspondent banking — was no longer guaranteed. It was conditional. The conditions were set by the EU and enforced by US secondary sanctions through OFAC.
Getting cut off didn’t just create an inconvenience. It severed a country’s standardised access to the currency that most of global trade runs on.
The Response
The weaponisation of SWIFT triggered exactly the reaction that sceptics had warned about. Countries that worried they might be next started building alternatives.
Russia had begun developing its own system — the System for Transfer of Financial Messages (SPFS) — back in 2014, right after it annexed Crimea and the first Western sanctions hit. At first it only connected around 400 Russian banks, but after the 2022 disconnections it expanded fast, reaching over 550 institutions across 24 countries.
China launched its Cross-Border Interbank Payment System (CIPS) in October 201536, designed to clear and settle cross-border payments in renminbi. By 2025, CIPS had 1,683 participants across 189 countries and regions, processing over eight million transactions a year37. Unlike SWIFT, which only carries messages, CIPS handles the money settlement itself.
Even the European Union tried to build a workaround. When the Iran nuclear deal fell apart, the EU started developing a system called INSTEX38 to let European companies keep trading with Iran without running into US sanctions. It failed. The transaction volumes never got anywhere near meaningful, because European banks refused to use it — they were too afraid that processing Iranian payments would trigger US secondary sanctions and cost them their access to dollar clearing39.
The architecture’s power didn’t come from law — it came from network dependency. No government order could force banks to risk their connection to the dollar system. Even SWIFT’s own home jurisdiction couldn’t build around it.
Meanwhile, BRICS nations ramped up bilateral agreements to settle trade in their own currencies40, cutting dollar-denominated systems out of the picture entirely.
The Replacement
The systems being built to replace SWIFT don’t just carry messages. They settle transactions directly, using programmable digital currencies where the conditions of the payment are baked into the payment itself. Two platforms are now under construction, and on the surface they look like they belong to opposite sides of a geopolitical divide.
The first is mBridge41 — a cross-border digital currency platform built by the central banks of China, Hong Kong, Thailand, the UAE, and Saudi Arabia. It’s already processed over $55 billion in transactions42, with China’s digital yuan making up 95 per cent of that volume. It does what SWIFT does — routes international payments — but faster, cheaper, and completely outside Western control.
The second is Project Agorá43, launched by the BIS with seven Western central banks including the Federal Reserve, the Bank of England, the European Central Bank, and the Bank of Japan44. Phase one is due to be finished in the first half of 202645. Agorá is built around the BIS’s ‘unified ledger’ concept: tokenised assets, programmable contracts, and both central bank and commercial bank money all living on a single platform.
In October 2024, the BIS quietly stepped back from mBridge — saying the project had reached ‘minimum viable product’ stage and was graduating from the Innovation Hub. This happened the same week Russia proposed ‘BRICS Bridge’ at the Kazan summit46 as a rival international payment system.
BIS general manager Agustín Carstens publicly distanced the institution, saying: ‘mBridge is not the BRICS bridge. We cannot work with sanctioned countries’47.
The BIS then shifted its resources to Agorá.
The obvious reading is that mBridge serves the East and Agorá serves the West — two blocs, two settlement systems, mirroring the geopolitical split.
Every major country along the India-Middle East-Europe Economic Corridor (IMEC) is hedging between the two. The UAE completed the first government digital currency transaction on mBridge with China in November 202548 — the same UAE that signed the Abraham Accords and is a core partner in IMEC. Saudi Arabia joined mBridge in 2024 — the same Saudi Arabia whose rail network forms IMEC’s land bridge.
But the deeper reading is that the competition is over who controls the routing, not the underlying standards. Both mBridge and Agorá are built on programmable digital currency infrastructure. Both use tokenisation at the individual transaction level. Both embed compliance conditions directly into the payment itself. Both require participants to meet technical interoperability standards — and in every case, those standards trace back to the same source.
The BIS’s Committee on Payments and Market Infrastructures49 (CPMI) works with IOSCO to set the principles that govern financial market infrastructure. The ISO 20022 messaging standard50 — which both platforms use — is managed through processes where the BIS and its member central banks hold the deciding influence.
So the BIS didn’t actually lose control when it stepped away from mBridge. It had already set the technical framework that mBridge was built on. The standard-setting function and the day-to-day operational function had been separated by design.
The Transaction Layer
The question raised earlier — whether conditionality would eventually reach down from countries and institutions to individual transactions — already has an answer in development.
Project Rosalind51, built by the BIS Innovation Hub’s London Centre with the Bank of England, lays out a retail CBDC API that can approve, deny, or modify a transaction at the moment of payment — before it goes through. The decision is based on who’s paying, what they’re buying, where they are, when they’re buying it, and how fast they’re spending. The conditions come in the form of ‘policy bundles’ that an authority pushes into the system.
The key mechanism is what’s called a three-party lock. With normal money, a transaction needs two parties — the buyer and the seller — to agree. With programmable money, a third party sets conditions that both sides have to satisfy before the payment clears. That third party is whoever writes the policy bundle: a compliance rule, an environmental metric, a spending cap, a restriction on certain categories of goods. The buyer has the money, and the seller is willing to sell. But the money won’t move until the condition-setter’s requirements are met.
In a sense, none of this is completely new. Third-party conditions on transactions already exist — OFAC sanctions lists, compliance filters at correspondent banks, FATF reporting rules. The difference isn’t that a third party is involved. It’s the speed and precision of enforcement. In the current system, compliance is checked by banks and other institutions, and it can be worked around through alternative channels. With programmable money, compliance is checked by the token itself — instantly, at the speed of the transaction, with no workaround available within the regulated system. The enforcement becomes total.
SWIFT carried messages between banks, and it could be weaponised by cutting a country off from the network. The systems replacing it carry value directly and embed conditions in the currency itself. The enforcement tool is no longer exclusion from the network. It’s the conditions written into the money before it’s allowed to move.
The Clearinghouse Pattern
SWIFT’s story follows a pattern that’s been repeating for two hundred years.
In the early 1800s, the Rothschild family cleared payments between nations privately, using their own couriers and coded letters. The job was done by a family, visible to the people who used it, and governed by business relationships. In 1844, the Bank Charter Act centralised domestic clearing through the Bank of England52. In 1930, the BIS extended that same model to work between countries.
SWIFT was the next version. Founded in 1973 — two years after Nixon closed the gold window and money lost its physical anchor — it took the messaging function connecting the world’s banks and put it into a cooperative utility that operated beneath the level of official regulation. For thirty years, it worked as neutral infrastructure. Then, starting in 2012, it turned out the infrastructure could be used as a weapon — because controlling the messaging layer meant controlling who got to participate in the global financial system.
mBridge and Agorá are the version after that. The messaging layer is being folded into the settlement layer. The instructions and the money they describe are merging into a single programmable token. The clearinghouse is no longer a separate institution sitting between two parties — it’s built into the money itself.
At every stage, the same function moves into a new form: from private couriers to institutional clearing, from institutional clearing to cooperative messaging, from cooperative messaging to programmable money. And at every stage, the infrastructure gets harder to see, harder to opt out of, and harder to hold accountable — because the people who write the rules and the people who enforce them keep getting further apart from each other.
Today, the media is busy drumming up the conflict between the West and BRICS. But although the geopolitical conflict, at least to a certain extent, is real, that doesn't actually matter in the end.
The question isn’t which platform wins. It’s who writes the standards that both platforms have to follow. The clearing function has migrated five times in two centuries. Each time, the institution that set the standards for the new form inherited the position that the previous institution had held. The BIS now sits in that position — because the technical frameworks it controls are what every platform has to conform to if it wants to plug into the global financial system.






















Again, the best reading on SubStack. The greatest hope in overcoming these gatekeepers is awareness. Thank you for opening our eyes.
Your essay on the evolution of SWIFT and the architecture of digital financial control is valuable — but it also unintentionally maps something else: the parallel, unwritten history of the global shadow networks that have grown alongside these systems. I don’t mean this cynically. I mean that your analysis reveals the visible layer, while an invisible layer has been expanding in the dark for years.
That invisible layer is now industrial in scale.
Across North Korea, Russia, China, Myanmar, Cambodia, Laos, the Philippines, and many other jurisdictions, industrialized digital‑asset extraction has become a studied discipline. What we call “fraud” or “scams” is, in reality, a mature global industry with training pipelines, specialization, and state‑aligned protection. OFAC, FBI, and other agencies have documented fragments of this, but the full picture is far larger.
In my own work, I’ve identified 15 fatal asymmetries that make this possible. One of the most dangerous is the massive competence gap between builders and users. That gap is a perfect window for sabotage — exploited not only by criminals, but sometimes by the builders themselves, often without users having any awareness of the risks embedded in the tools they rely on.
What you are describing is, in effect, the history of the digitization of usury.
And here is the paradox: As long as digital tools remain controlled by a small technical elite, digital usury can operate with near‑total opacity. But the moment ordinary people begin using these tools with skill and autonomy, the system becomes impossible to run without spawning enormous shadow networks of digital “artists,” extractors, and opportunists. Today, those shadow networks are growing faster — and with more competence — than the so‑called legitimate systems attempting to centralize global financial control.
So the real question becomes: Who is actually building the shadow digital system? Is it a revival of cyber‑punk ethos? Is it opportunistic theft? Is it a form of digital warfare? Or is it simply the natural evolution of unregulated digital capitalism?
I don’t know the answer. But I do know the scale: industrial.
And I know this: the digitized offshore economy — controlled by actors whose identities are unknown — is measured in dozens of trillions. Any attempt to build a new global digital financial regime will have to confront this reality before it can claim to be “safe.”
To illustrate the structural shift:
Traditional Usury Model LENDER ← interest → BORROWER • Known parties • Disclosed terms • Legal recourse • Regulated rates
Crypto / Stablecoin Usury Model HIDDEN PRINCIPALS ↓ extraction SHELL COMPANIES (exchanges) ↓ fees, spreads, liquidations VISIBLE “FOUNDERS” (sometimes fronts) ↓ marketing INFLUENCERS / MEDIA ↓ “education,” “community” RETAIL BAGHOLDERS ↓ when broke NOWHERE TO GO
• Unknown extractors • Undisclosed terms • No recourse • No rate limits • 24/7 extraction • Global scale
Given the choice between “fat bankers,” former cyber‑punks, gamers, or a construction worker, I’ll follow the construction worker — the builder — every time. Builders understand structure, failure modes, and real‑world constraints.
Ultimately, I want usury abolished or at least made consent‑based. Without that, any digital financial future will simply reproduce the same power asymmetries — only faster, more opaque, and more dangerous.